
ESET Home Products for Windows Version 12.0.27.0 Have Been Released
Release Date: October 23, 2018 ESET NOD32 Antivirus, ESET Internet Security and ESET Smart Security Premium version 12.0.27.0 have been released and are available to download. Changelog: Added: Referral program Improved: Activation wizard improvements Improved:...
Would you neglect to maintain your car? If you did, would you be surprised if it broke down?
Would you neglect to maintain your car? If you did, would you be surprised if it broke down? Then, why do you neglect routine maintenance and tune-ups for your computer?? Most people are accustomed to doing regular oil changes, brake pad maintenance and more for their...
Cyber Monday Bundle Sale: Save 25% on Antivirus and Backup Bundles!
Bundle your New ESET or PC Matic Home Antivirus with Backup and Save 25% in our CyberMonday sale. Offer applies to all ESET home products, all PC Matic Home licenses and with backup. Cyber Monday Bundle Sale!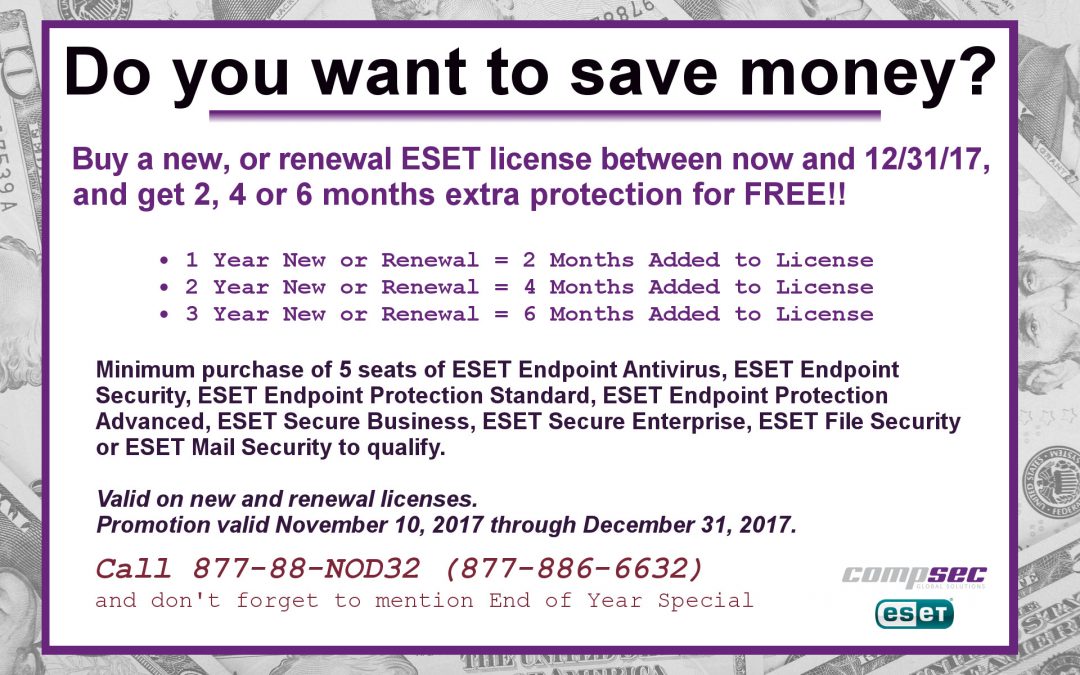
ESET end of Year Promo: 2, 4 or 6 months FREE on New and Renewals!
ESET is currently offering 2, 4 or 6 months free on 1, 2 and 3 year new or Renewal licenses. This is an incredible savings – the best deals are obviously on the 3-year new and renewal purchases, but if you can bring your purchase through between now and the end...
Replace your Kaspersky with an ESET Home Product and Save!
In the light of recent allegations regarding Kaspersky Lab possibly being involved in NSA hacking, or at least being in posession of stolen NSA hacking tools, we have received a number of requests for specials from owners of Kaspersky software. The first special we...Spam threat to DDoS your website on September 30th
Did you just get an email that looks like this? If so, don’t panic. Many thousands of companies around the world are believed to have received emails in the last few days to a week, claiming to come from “Phantom Squad” with the subject line “DDoS Warning”. The...
Patch This Windows 0-Day Flaw That’s Being Used to Spread Spyware
Get ready to install a fairly large batch of security patches onto your Windows computers. As part of the September Patch Tuesday, Microsoft has released a massive raft of security updates to patch 81 CVE-listed vulnerabilities, on all supported versions of Windows...ESET Banking and Payment Protection: How to Add a website to ESET Banking & Payment protection
This video demonstrates how to how to add a banking website to the list of sites secured by ESET Banking & Payment protection. By default, most major banking websites will automatically give you the option to continue in a secured browser. If your website is not...
